> NETWORK SECURITY
The first line of defence for your network is your firewall. The more unwanted and malicious traffic you can block here the better. Your firewall will never be able to stop everything getting into your network, this will inhibit your ability to function as a business. However, with next generation firewalls (NGFWs) incorporating a variety of different functions such as advanced malware protection (AMP), content filtering, next generation IPS (NGIPS) to name a few, firewalls are becoming much better at allowing the good and blocking the bad.
Every day malicious actors are coming up with new methods and exploits for circumventing perimeter devices, therefore its important your firewall stays up to date.
In todays personal data climate, with increased regulatory pressures in the form of GDPR, its essential to have a feature rich, but most important CORRECTLY CONFIGURED device in order to stop malicious activity in its tracks. A potential breach is not only damaging to reputation, but could cost your business a lot of money if your security is not up to standard.
Traditional packet filter firewalls simply do not cut it anymore (these are firewalls that can only filter based on where the traffic comes from, or where it’s going to.) It’s far too easy for attackers to disguise malicious traffic as something trustworthy.
This is where firewalls have had to up their game, by inspecting deeper into the traffic that comes in from the internet, and out from your network.
There are certain technologies where perimeter firewalls and endpoint security overlap – for example, its perfectly possible to have an application/layer 7 firewall built into your perimeter firewall, as well as malware detection, IPS etc.
The key to a solid security policy is LAYERS OF SECURITY within your organisation. For example, if traffic were able to penetrate your perimeter firewall, your endpoint security solution would detect and quarantine it. The more layers of security, the more secure your network becomes, however too many layers may become too difficult to administer. This is where our security specialists come in, to provide you with a bespoke solution based on your requirements, to ensure you find the correct balance between security and simplicity.
JARGON BUSTER! Below is a list of some common network security threats and attacks. Click on the links to reveal the explanations.
A potential hacker sends especially crafted data packets to your firewall to determine what ports are open (these are virtual ports, not physical ports) based on the replies received. By seeing which ports are open, an experienced hacker begin to probe these ports with further attacks to try to gain entry to your network. Certain port numbers are used for certain services (eg: TCP port 443 is HTTPS – secure HTTP, the protocol used for secure web browsing), so a hacker can determine what services are running behind your firewall.
Any attack which prevents an application from performing its service. In the case of a firewall, sending too much traffic for the firewall to process will cause the firewall to become unavailable to process legitimate traffic. A common denial of service attack comes from more than one source, and is called a distributed denial of service (DDoS) attack. Malicious software in installed on unknowing victims machines, and is orchestrated from a central location (see botnets.) This can generate incredible amounts of traffic from thousands to hundred of thousands of locations.
Firewalls are configured to allow traffic from specific sources and deny traffic from anywhere else. If a packet is crafted to have its source spoofed to a whitelisted address, the packet will bypass the firewall and reach its destination, (obviously there will be no return traffic as the firewall will return traffic to the legitimate address destination) however a single packet or stream of packets can still cause considerable damage to a network.
Malicious payloads are sent in fragments to pass through the firewall and past defences, to be re-assembled as their destination.
Malicious software is installed on multiple devices, unbeknownst to the user. The software allows command from a central location, allowing a hacker to control all devices from a central place. From here a distributed denial of service attack could be deployed, or other forms of distributed attacks.
Packets between 2 locations is collected and analysed to determine what traffic is being passed. Unencrypted traffic is susceptible as traffic sent in plain text can be read without any issue by the attacker. Unencrypted protocols such as HTTP, FTP and telnet are vulnerable as any user credentials sent over these services can be collected and stolen.
Out of date firewall firmware may be vulnerable to discovered exploits or bugs. Exploits are available online if you know where to look for them, so any out of date firmware running on firewalls can be attacked to gain access or perform a denial of service attack.
Phishing attacks are when seemingly legitimate emails are sent with a malicious intent. It may be a link that you are encouraged to click on, an attachment you are encouraged to open, or even just instruction to do something that you would normally do (such as transfer money to an account on request from a manager.) There are different types of phishing attacks depending on the target. Standard phishing attacks generally aren’t too specific in target, and the content of the email will be something that could apply to a large demographic of user. SPEAR phishing attacks are when the content of the email is designed to target a specific individual which will seem a lot more legitimate. WHALE phishing attacks are similar to spear phishing, except they are targeted as high level executive individuals.
Below are a list of networks security devices and protocols. The most common secure remote access protocols and firewall concepts are explained below:
A Virtual private network (VPN) provides secure remote access to a network over the internet. A site to site VPN provides connectivity between 2 networks and generally uses the IPSec protocol. A remote access VPN provides connectivity to a network from a single machine. Remote access VPNs can use both the IPSec and SSL protocols. The SSL protocol relies on digitally signed certificates to determine the trust of the network you’re connecting to, similar to when you visit an untrusted website in your browser. IPSec can also use certificates but can also use pre-shared keys known at each end of the connection, much like a password. VPNs allow you to work from anywhere in the world (as long as there is an internet connection) as if you were in the office.
A hardware device or software application, that filters traffic based on the source, destination and port of the traffic.
A firewall device that includes several other security technologies, such as advanced malware protection, NGIPS and content filtering. We would recommend that NGFW’s are the only devices that should be implemented at the business level moving forward.
Next generation intrusion protection systems (NGIPS) analyses traffic at the network level, compared to antivirus that analyses files. This allows it to baseline the network to discover what normal day to day network traffic looks like, then can notice and block any anomalies before they cause any problems. Part of the NGFW setup, although you can have NGIPS as a standalone service too.
A hardware or software device (can even be hosted in the cloud) that analyses incoming mail and blocks anything it deems to be spam (junk mail.) Spam filters are a must have and can stop your mailbox getting bombarded by potentially harmful, irrelevant mail.
High availability (HA) is a service that works between 2 devices, that allows for uninterrupted service. 2 identical devices run alongside each other, with the same configuration, and can take over from each other instantly if one device were to fail. This allows for seamless failover and a high level of redundancy, especially if combined with a failover internet circuit.
Software defined wide area networking (SD-WAN) requires more than one internet circuit (unless managed as the ISP end) and allows for the customisation of outbound traffic dependant on metrics such as bandwidth, latency, speed etc. It can pro-actively monitor the circuits to determine which circuit is performing the best at the time, and can switch traffic between them based on which is functioning the best at the time. An example might be using a certain circuit for voice traffic due to its dependency on a low latency/packet loss level, and using the other circuit for web browsing, due to the relatively low impact it would have on searching the web. SD-WAN is becoming more and more common and is a great feature not only for performance, but also for redundancy. Due to its generally lower cost and higher level of customisation, companies have been replacing their legacy MPLS circuits with it, although MPLS does still have its use cases.
Advanced malware protection (AMP) goes a bit further than traditional anti-virus in its techniques for identifying malicious files. It can detect all forms of malware, and has additional functionality such as sandboxing, and in the case of Cisco, can compare the file to the Cisco TALOS database. It also doesn’t stop at just the initial inspection, it will continue to monitor the behaviour of the file once it has entered the network. AMP should be the standard at both endpoint and network level.
> WHAT WE OFFER
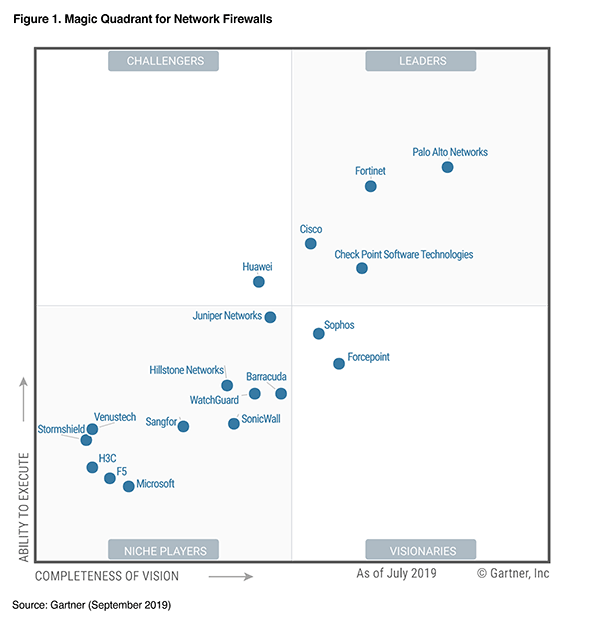
ackio offers a variety of options, when it comes to security. We only claim to support a vendor when we’ve actually tried and tested in house, learned thoroughly and have been accredited in the solutions. So you can be sure you’ll receive a high standard of remote support if required. While not limited to, below are examples of vendor firewall solutions we offer, along with their pros and cons and recommended environments.






Cisco’s NGFW range consists of the adaptive security appliance (ASA) and the firepower appliances. The ASA is the base firewall device, and these devices have FirePOWER modules within them as virtual machines. This allows for the upgrading of the base firewall to a NGFW, and each individual component can be licenced as required. ASA modules range from the entry level 5506-X to the enterprise level 5555-X. They also offer data centre level appliances in the form of the firepower appliances. To learn more about their features and models, you can visit the relevant documentation here. They also offer virtual instances of their ASA and firepower appliances that can be run using your own infrastructure.
Even though these are enterprise grade firewalls, we would still recommend the small models for smaller businesses, however the licences for the NGFW features come at an extra price on top of the device. They are incredibly feature rich, so its advised they are installed and configured by an accredited engineer.
Meraki (bought by Cisco in 2012) are a software defined networking vendor, who’s solutions are excellent for ease of administration and simple plug and play installation. All configuration for these devices is done in the cloud, and pulled to the device via the internet. They originally started out offering only cloud managed wireless, but have since released firewalls, switches, CCTV and monitoring software. Their firewall offering consists of the smaller MX64, to the enterprise grade MX450. They also offer the vMX100, a virtual appliance that can be run on your own infrastructure. To learn more about the models and their specifications, click here. They work on a subscription basis, and include AMP, IPS and content filtering with the advanced security licencing. The Meraki MX range also have SD-WAN capabilities in built as standard.
We would recommend these for the education sector, as when incorporated with devices from the entire Meraki portfolio, they offer a centralised dashboard for the management on the entire network, as well as integrating with each other across the devices. In built client monitoring and reporting is also a very important feature in education, that Meraki performs as standard
Sonicwall (previously Dell Sonicwall) are exclusively dedicated to security. The functionality of their solutions are built from the ground up with security as the main principle, ensuring that the security of your network is never compromised. As with Cisco, they have a range of devices from the smaller SMB sized business, right up the data centre levels of throughput required. More information about their models and specifications can be found here. With built in AMP, content filtering, IPS and their bespoke Real-Time Deep Memory Inspection (RTDMI) and Reassembly-Free Deep Packet Inspection, the Sonicwall solutions are capable of inspecting encrypted traffic in real time, to search for anything malicious masquerading as legitimate traffic. They are also capable of having in built spam filters, and as with Meraki, have in built SD-WAN and high availability capabilities out of the box.
We would recommend Sonicwall firewalls for small to medium sized businesses, looking to get the most bang for your buck. The ease of administration is at an intermediate level, although its fairly intuitive once you begin to use it. Their security centre is also something to behold, with a geographical live view of worldwide threats.
Below is a list of other firewall vendors we support:
-
Juniper
-
Sophos
-
Fortinet
-
pfSense
-
Draytek
-
Zyxel
We also support the below on a best endeavours basis:
-
F5
-
Checkpoint
-
Watchguard
-
Palo Alto